
Share
How to Disable Automatic Login in Windows 10
This likely isn’t a problem if you’re at home all the time, but if you have a laptop this becomes a serious security risk. Especially if you travel with your laptop. This automatic login means that anyone who finds your computer (or steals it!) only needs to start it up to have access to all your files. Because of this, companies that have information security policies typically mandate that you disable automatic login on your Windows 10 machine.
How To Disable Automatic Login:
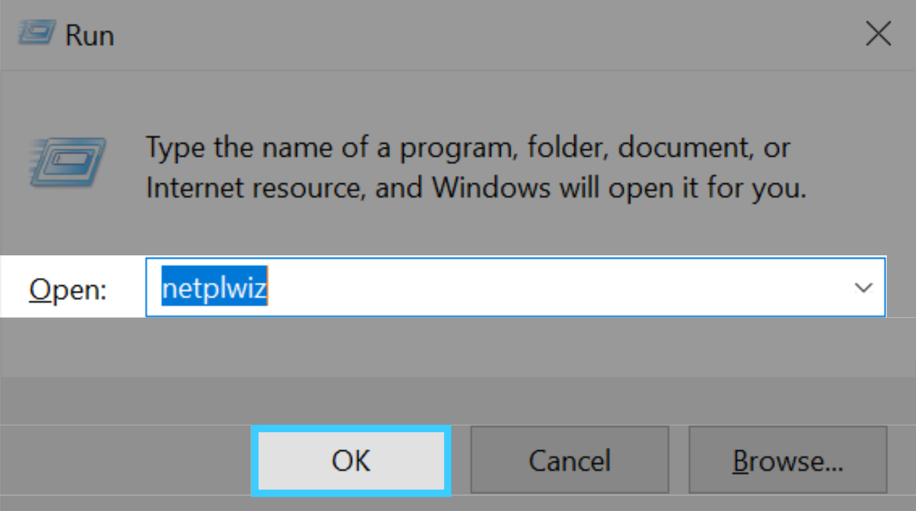
Step 1: Press Win+R, enter “netplwiz“, which will open the “User Accounts” window. Netplwiz is a Windows utility tool for managing user accounts.
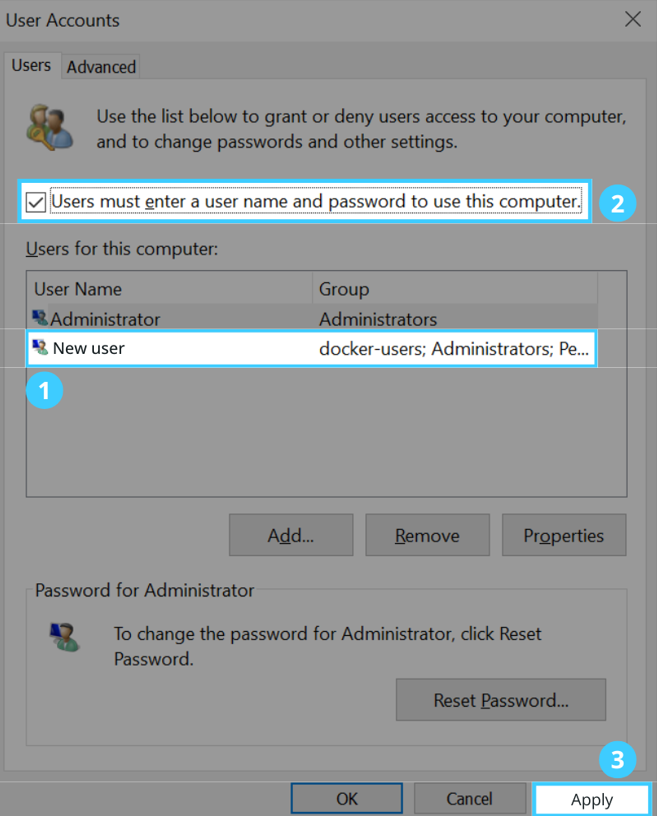
Step 2: On the “User Accounts” window, select the user account and check the option for “Users must enter a username and password to use this computer” and then click Apply.
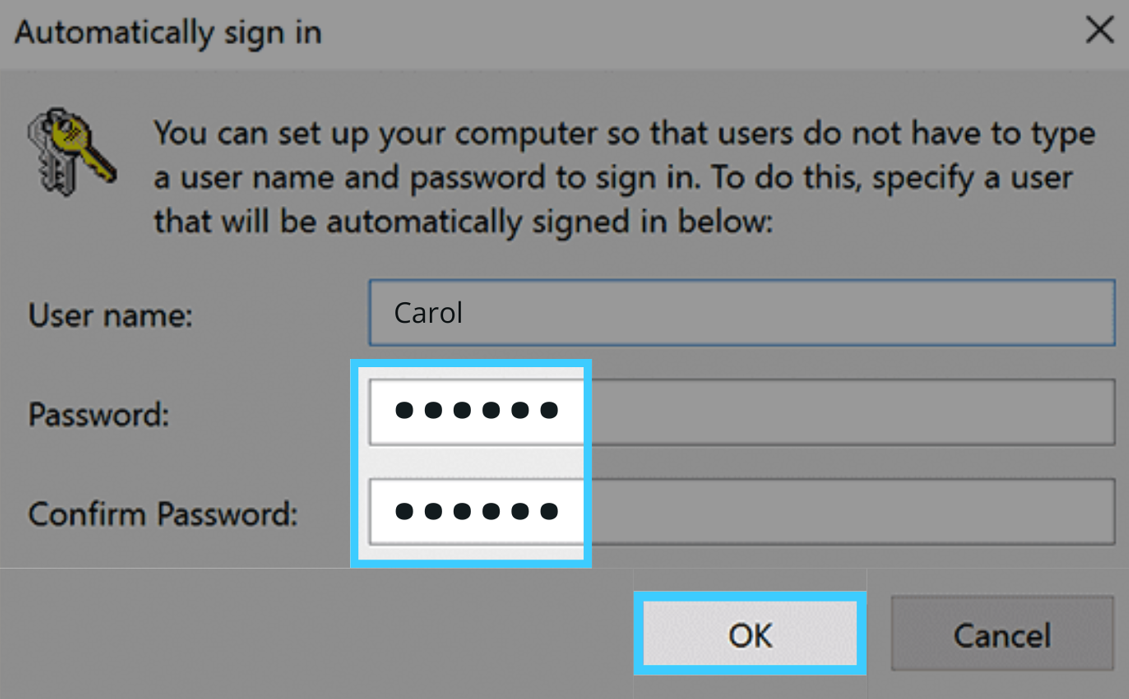
Step 3: If the sign in dialog appears, enter your user name and password and subsequently click the 'OK' button.
Step 4: That's it! You've successfully disabled auto login on your Windows 10. Restart your computer and the system will prompt you to enter your password at the login screen.
Why Small Steps are Important for Keeping Your Company Secure
The information security policies and procedures at your company are incredibly important. Even on your personal computers at home, following these policies can help make sure your own information stays safe! Everyone should be aware about how to protect their own personal and financial information at home. You don’t want to be a target of identity theft. Or the source of a data breach at your company!
In the case of your Windows 10 laptop set to log in automatically that’s what we InfoSec experts consider an endpoint. Every laptop or device that remotely connects to your corporate network or systems is called an “endpoint,” which means these devices are all a potential entry point for security threats. While that automatic login feature is convenient, it also makes your laptop more vulnerable.
Get Cybersecurity Policies for Your Business
If your company already has policies, make sure you’re familiar with the requirements and follow them. Go find them. You’ll want to stay up to date since companies change and update their policies. If you have a small business or startup you will likely have to create your own security policies.
It doesn’t matter if you’re a salesperson, a marketer, or a developer with access to everything. You don’t have to work in IT. You’re a target. Unfortunately, too often small businesses are easy targets. Most cyber attackers don’t discriminate. They’ll hit with a broad stroke. In fact, they might target every employee with an @YourCompany.com email address. Or every device connected to your company wifi network.
Cyber-attacks may target and steal your employee personnel records. Other times, the target is your company’s customer database full of private records, payment information, passwords, and internal data. However, your company may not be the true target, if you are a vendor for a global brand or Fortune 500 company.
If your laptop or another endpoint is compromised, that could give someone with nefarious intent access to other devices, databases, and critical systems within your company. Securing every possible entry point, through easy steps like disabling automatic logins, is key
 Back
Back











 Linkedin
Linkedin








