Share
Artificial Intelligence (AI): The Vanguard of Cybersecurity Space
The cybersecurity landscape is no stranger to emerging technologies and tools! Especially, Artificial Intelligence (AI) has proven itself to be a powerhouse with its ability to break massive datasets, identify patterns, and produce accurate decisions. These decisions have been transforming the way cyber threats and attacks are being avoided and nullified, thus making AI-powered cybersecurity a much bigger powerhouse!
The highlights of the report titled ‘PwC’s 2024 Global Digital Trust Insights’, which surveyed 3,876 business, technology, and security executives across the world with 136 participants from India, further add to the significance of AI in cybersecurity. As per the report, more than two-thirds (69%) said they would be using Generative AI (GenAI) for cyber defence in the next 12 months, while nearly half (47%) of them are already using it for cyber risk detection and migration.
The Generative AI Preference
In 2023, AI was largely deployed by organizations around the world on various fronts, thus standing in the vanguard of the cybersecurity space. The tech giant Google has brought GenAI into cybersecurity with its Sec-PaLM, an AI model trained on security use cases. This AI model helps analyse malicious scripts and detect the most threatening ones. To further comprehend threat intelligence, Microsoft’s Security Copilot leverages the GenAI model from Open AI called GPT-4 to process threat signals and fight against new threats and vulnerabilities. These niche products highlight the benefits of AI in cybersecurity, while many more companies are harnessing the power of AI to enhance efficiency and explore new ways to achieve utmost growth.

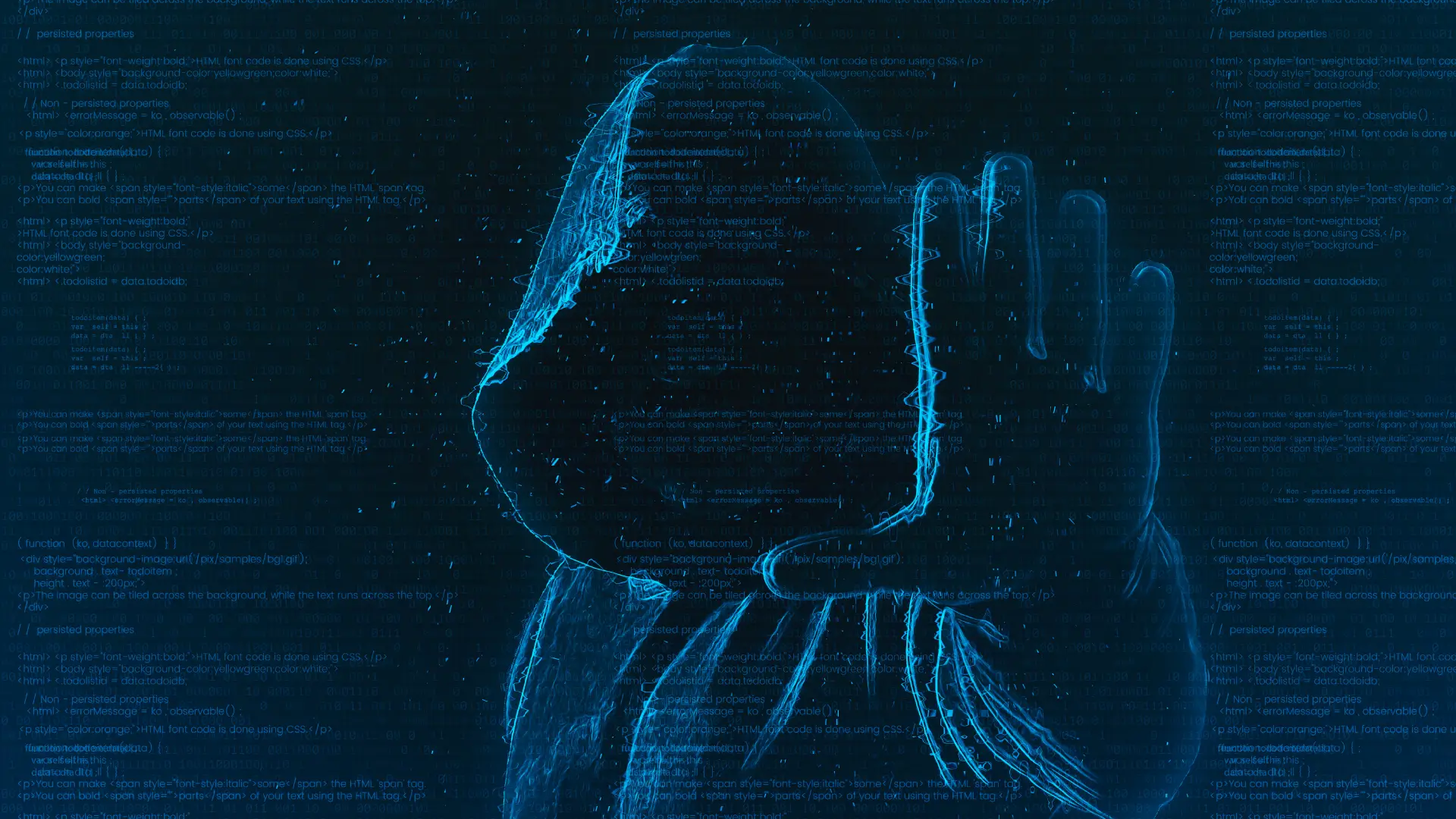
As we near the end of 2023, the adoption of GenAI in cybersecurity is one of the biggest trends we expect to behold. Since cybercriminals have been using AI for email phishing scams, ransomware, and many other cyber threats and attacks, cybersecurity professionals must battle AI with AI. Unlike the traditional advantages of AI in cybersecurity, GenAI can proactively detect, protect, and mitigate huge volumes of cyber threats and attacks.
Having comprehended the importance of GenAI and its related tools, most cybersecurity teams are looking to embed it into their processes and systems. Some of the most promising areas for deploying GenAI in cyber defence entail cyber threat detection & analysis, cyber risk and incident reporting, customized security policies, and prevention of data breaches.
1. Cyber Threat Detection & Analysis:
With the advent of GenAI, organizations are adhering to a proactive approach to cybersecurity rather than a reactive approach after the occurrence of threats. A GenAI model, which is trained on vast amounts of cybersecurity data, can learn from patterns found in cyber threats and attacks, thus predicting future threats in advance.
The biggest advantage of the GenAI adoption is swift detection and response times with regard to cyber-attacks and threats, thereby enabling cybersecurity professionals to make quick, pre-emptive decisions. Besides, GenAI can also secure systems by generating complex, unique, and secure passwords, or encryption keys for them, thereby providing an additional layer of security against data breaches.
2. Cyber Risk & Incident Reporting:
With the rise in the number of cyber threats, malware, password thefts, traffic interceptions, phishing attacks, ransomware, loopholes in existing security infrastructure, and many other cyber risks, cyber incident reporting outclasses as an indispensable tool for companies to learn about the cyber incidents and enhance their risk management strategies. It is here that GenAI plays a pivotal role in making the entire process of cyber risk and incident reporting a simpler one.
Leveraging the best of Natural Language Processing (NLP), a branch of AI, GenAI can transform complex, technical data into succinct content that even non-specialists can comprehend. Besides incident reporting, this technology can help with threat intelligence, risk assessments, alert triage, phishing detection, user behaviour analysis, and many other tasks by creating simple text that anyone can understand. Also, GenAI helps in generating incident reporting protocols that enable employees to report any potential GenAI-related threat and vulnerability seamlessly.
3. Customized Security Policies:
GenAI extends its capability to draft customized and holistic security policies and standards in accordance with the organization’s cyber threat profile and business objectives. This technology also ensures that security policies and standards are updated on a constant basis, thus heightening the security of the IT environment in the organization. Furthermore, organizations can stay watchful of the ever-evolving cyber threats and vulnerabilities by adhering to an adaptive approach based on GenAI technology.
4. Prevention of Data Breaches:
Organizations can protect sensitive information and data from data breaches or leakage by deploying GenAI to generate new, synthetic data that mimics real-world data. This synthetic data consists of data points that hold similar patterns as that of the original data but without the inclusion of any original data. Hence, organizations can meticulously execute tests and simulations without exposing the sensitive data and information available in the original data.
GenAI: A Boon-Bane Technology
Besides the above defensive approaches to cybersecurity, GenAI has also been used as an offensive approach by cyber attackers for various nefarious activities. Right from creating phishing emails, fake login pages, or websites akin to the authentic ones to generating self-learning and constantly evolving malware codes, misleading deepfake videos, audios, and images, and much more, GenAI has stood out as a bane as well. Hence, organizations are in constant pursuit of making AI the linchpin of their cybersecurity strategies and policies as cyber attackers have been exploiting the might of this technology to redefine their techniques and enhance their attacks and threats. In a nutshell, battle AI with AI!
The usage of AI in improving our response to threats has been a game changer in the field of cybersecurity. We at Cloud Destinations’ Security Team are focused on enabling the Security Operations team to respond effectively with AI/LLM-based approaches. These approaches have provided us with suggestions on different mitigation tactics that helped in reducing our Mean Time To Respond (MTTR). Our research in deploying OpenAI to deliver threat intelligence by tracking malicious actors and attack patterns is a work in progress!

If our take on leveraging AI in cybersecurity inspired you, feel free to learn more about our services, solutions, management, work culture, and others by tapping this link - https://clouddestinations.com or writing to us at info@clouddestinations.com with any query or suggestion. Rest assured that your queries will be duly answered!
 Back
Back











 Linkedin
Linkedin








